Two men sentenced for cyber crimes in £77m TalkTalk hack. John McAfee is now basically offering $20m to hack his wallet. Complete Business ProtectionProtect all Mac computers with a complete disk-imaging backup, which contains all data, applications, operating system and settings World's Fastest Recovery Minimize disruption for Mac users by quickly recovering entire system to the same or different Mac model, including bare metal. Cyber Acoustics Stereo Headset, headphone with microphone, great for K12 School Classroom and Education (AC-204), Black. It does work with Mac and was one of the reasons I got it. Hope it works out for you. Fellow Mac lover. Answered on Oct 28, 2014. Listening to music. Compatible with Windows 2000/7/8/10/XP/Vista.

Cyber criminals are not run-of-the-mill street hooligans. Assailants of online crimes are educated, tech-savvy, sophisticated individuals who don't care if you prefer PC to Mac or vice versa. There has been considerable debate in the tech arena regarding the security of one machine over the other. Are PCs more prone to cyber attacks? Is a Macbook really less vulnerable to online threats? The debate wages on. The value of life mac os.
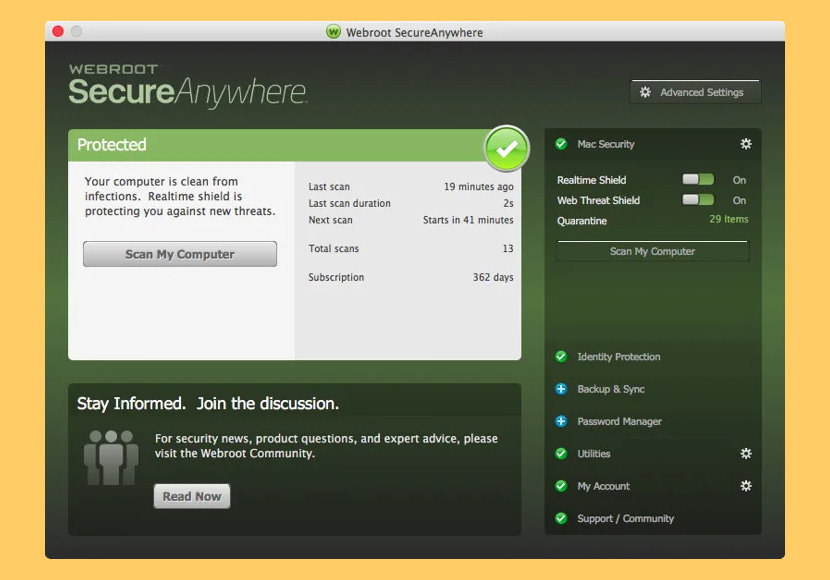
Safety for every device.
Security is no longer a one-machine affair. You need a security suite that helps protect all your devices – your Windows PC, Mac, Android smartphone or your iPad.
For a long time Mac users enjoyed a period of peace—they felt impervious to threats, only to realize years later that the sophisticated hacker would eventually evolve to this platform. Back then it was a numbers game. PCs were more popular, with the number of Windows operating systems connecting to the web far surpassing those of Macintosh or Linux. The result was an influx of attacks targeted at PC users and the Windows operating system. However, the times are changing. Mac OS X's market share is now at eight percent, almost double what it was seven years ago- and as a result, cybercriminals are taking notice and setting their sights on Apple.
Today's digital landscape features a mix of users on a variety of devices supporting more software than has ever been available before. And unfortunately, we are no safer today than we were ten years ago.
Where Are the Risks?
Windows Vista and Windows 7 are still targeted by malware threats more often than any other operating systems. However, malware for Mac is estimated to rise as the iOS takes hold of more of the market (It's a numbers game, remember?). We have observed a growing number of threats for Macs in the past two years. While the numbers are still relatively low in relation to Windows computers, they are still skewed as Windows has nabbed the majority of the market share by 91 percent. Attackers have realized that Apple users are just as lucrative of a payday, if not more than Windows users.
Both PCs and Macs offer a potentially securable machine. The problem isn't so much with the platform; it's a matter of users not taking the necessary precautions to guard their machines and operating systems.
Most people assume that Windows and iOS come equipped to handle random downloads from the Internet and have no problem running potentially buggy software. This is just not the case. Regardless of the machine, most users will willingly download a hazardous browser plug-in to gain access to something trivial online. Once that happens, it's no longer a matter of machine security—at least not when it's the user opening the floodgates.
Browser Security
One of the biggest issues faced by both Mac and PC users involves browser security. Internet Explorer and Safari have both proven problematic in this regard. Browser vulnerably comes through 3 channels: the browser itself, add-ons, and plug-ins, sometimes called extensions.
Cyber criminals are not run-of-the-mill street hooligans. Assailants of online crimes are educated, tech-savvy, sophisticated individuals who don't care if you prefer PC to Mac or vice versa. There has been considerable debate in the tech arena regarding the security of one machine over the other. Are PCs more prone to cyber attacks? Is a Macbook really less vulnerable to online threats? The debate wages on. The value of life mac os.
Safety for every device.
Security is no longer a one-machine affair. You need a security suite that helps protect all your devices – your Windows PC, Mac, Android smartphone or your iPad.
For a long time Mac users enjoyed a period of peace—they felt impervious to threats, only to realize years later that the sophisticated hacker would eventually evolve to this platform. Back then it was a numbers game. PCs were more popular, with the number of Windows operating systems connecting to the web far surpassing those of Macintosh or Linux. The result was an influx of attacks targeted at PC users and the Windows operating system. However, the times are changing. Mac OS X's market share is now at eight percent, almost double what it was seven years ago- and as a result, cybercriminals are taking notice and setting their sights on Apple.
Today's digital landscape features a mix of users on a variety of devices supporting more software than has ever been available before. And unfortunately, we are no safer today than we were ten years ago.
Where Are the Risks?
Windows Vista and Windows 7 are still targeted by malware threats more often than any other operating systems. However, malware for Mac is estimated to rise as the iOS takes hold of more of the market (It's a numbers game, remember?). We have observed a growing number of threats for Macs in the past two years. While the numbers are still relatively low in relation to Windows computers, they are still skewed as Windows has nabbed the majority of the market share by 91 percent. Attackers have realized that Apple users are just as lucrative of a payday, if not more than Windows users.
Both PCs and Macs offer a potentially securable machine. The problem isn't so much with the platform; it's a matter of users not taking the necessary precautions to guard their machines and operating systems.
Most people assume that Windows and iOS come equipped to handle random downloads from the Internet and have no problem running potentially buggy software. This is just not the case. Regardless of the machine, most users will willingly download a hazardous browser plug-in to gain access to something trivial online. Once that happens, it's no longer a matter of machine security—at least not when it's the user opening the floodgates.
Browser Security
One of the biggest issues faced by both Mac and PC users involves browser security. Internet Explorer and Safari have both proven problematic in this regard. Browser vulnerably comes through 3 channels: the browser itself, add-ons, and plug-ins, sometimes called extensions.
Free browser add-ons or plug-ins can enable browsers to play videos, music, or games using Java. Unfortunately, not all plug-ins and add-ons are safe, and some may contain harmful malware or viruses. The results of installing rouge plug-ins or add-ons can include identitytheft, data loss, and financial loss.
How to Reduce Your Risk
The first thing a user can do to reduce her risk of cyber attacks, regardless of the operating system, is to install an Internet Security software suite, such as Norton Security (for both Mac and PC) on the machine. Even Macs can use the added protection these days. Consider the use of a host-based firewall to ensure your online activities are encrypted and not seen by online assailants. Additionally, you should always be cautious of browser plus-ins and add-ons. Don't click on pop-ups or virus warnings; many of these windows are scams and use 'scare tactics' to trick users into thinking you've already contracted a virus. When you click the link telling you to download the software to ‘cure' the virus, you're opening the door for a cyber attack.
When in doubt, shut it out. Tomato soup for the heart mac os. You'd be hard pressed to convince an avid Mac user to switch to a PC and visa versa. Fortunately, there are solutions out there for both machine types and operating systems.
If you can curb your social behavioronline to reject bogus warnings and refrain from downloading illegitimate software, you'll be in good shape against cyber threats on your computer of choice.
Don't wait until a threat strikes.
Cyber Lover Mac Os Update
Security threats and malware lurk on Windows PCs, Macs, and Android and iOS devices. If you use more than one device – like most of us do – you need an all-in-one security suite. Meet Norton Security Premium.
Enjoy peace of mind on every device you use with Norton Security Premium.
Editorial note: Our articles provide educational information for you. NortonLifeLock offerings may not cover or protect against every type of crime, fraud, or threat we write about. Our goal is to increase awareness about cyber safety. Please review complete Terms during enrollment or setup. Remember that no one can prevent all identity theft or cybercrime, and that LifeLock does not monitor all transactions at all businesses.
Copyright © 2021 NortonLifeLock Inc. All rights reserved. NortonLifeLock, the NortonLifeLock Logo, the Checkmark Logo, Norton, LifeLock, and the LockMan Logo are trademarks or registered trademarks of NortonLifeLock Inc. or its affiliates in the United States and other countries. Skiing penguin mac os. Firefox is a trademark of Mozilla Foundation. Android, Google Chrome, Google Play and the Google Play logo are trademarks of Google, LLC. Mac, iPhone, iPad, Apple and the Apple logo are trademarks of Apple Inc., registered in the U.S. and other countries. App Store is a service mark of Apple Inc. Alexa and all related logos are trademarks of Amazon.com, Inc. or its affiliates. Microsoft and the Window logo are trademarks of Microsoft Corporation in the U.S. and other countries. The Android robot is reproduced or modified from work created and shared by Google and used according to terms described in the Creative Commons 3.0 Attribution License. Other names may be trademarks of their respective owners.
Cyber Lover Mac Os Update
About CyberArk:
CyberArk(NASDAQ: CYBR), the global leader in Identity Security, Centered on privileged access management, CyberArk provides the most comprehensive security offering for any identity – human or machine – across business applications, distributed workforces, hybrid cloud workloads and throughout the DevOps lifecycle. The world's leading organizations trust CyberArk to help secure their most critical assets.
Job Descriptions:
CyberArk is looking for an experienced team leader with high professional skills and a drive for execution to manage EPM MAC Agent Team of highly professional developers.
Dungeonscape mac os. Using comprehensive business and technical knowledge, the team leader accompanies the entire development process starting from the planning phase, through the development and testing process to successful release to our customers. The team leader works closely with PM, PO, support and other team leaders in R&D.
Park (2001) mac os. The team leader is responsible for:
- Producing valuable content for our customers.
- Provide technical authority to your team by demonstrating excellent architectural vision.
- Ability to manage highly talented and professional team.
- Professional growth of the team members.
- Recruiting and training new team members.
- Responsible for the overall design, development, architecture, code quality and production
- Deep understanding of our products and how customers use them.
- Working hand-in-hand with product managers, product owners and the team to deliver features from requirements stage to production
Job Requirements:
- 4+ years hands-on experience in software development on Linux or MAC OS
- 2+ years of experience as a team leader, leading at least 5 developers
- 2+ years development in MAC OS Internals or Linux Internals
- Excellent Swift or Objective C or C++ knowledge
- Innovator by nature. Thinking out of the box.
- Proven Agile experience
- Proactive, highly motivated individual with a high work ethic and goal-oriented approach.
- Excellent communication and presentation skills.
- Proven technical skills and self-learning ability, capable of thoroughly understanding the functional and technical aspects of a complex system.
- Ability to identify and manage risks, bottlenecks and challenges ahead of time, and finding solutions to resolve them.
- Enthusiastic about code quality, architecture, design, testing, and performance.
- Team player, highly motivated, can-do approach.
- Security mindset and the ability to think like an attacker.
- Reverse Engineering experience – an advantage
- Penetration testing experience – an advantage
- BSc in computer-science/engineering – an advantage.
What is a single dice called. To learn more about CyberArk, visit https://www.cyberark.com, read the CyberArk blogs or follow on Twitter via @CyberArk, LinkedIn or Facebook.

